South Africa’s Rail, Port and Pipeline Hit by Cyber Attack
Transnet, a state-owned South African rail, port and pipeline company, appears to be in crisis mode after a cyberattack hit the company last week. Keep Reading

Transnet, a state-owned South African rail, port and pipeline company, appears to be in crisis mode after a cyberattack hit the company last week. Keep Reading

Researchers with cybersecurity company SentinelOne reconstructed the recent cyberattack on Iran's train system in a new report, uncovering a new threat actor -- which they named 'MeteorExpresss' -- and a never-before-seen wiper. Keep Reading

Under the Immigration and Nationality Act, a noncitizen who is likely to become a public charge is generally inadmissible to

The United States, in concert with the United Kingdom, is imposing additional costs on the Russian Federation on the one-year

If you don't recognize Franklin by his name, you will, most likely, recognize two of his high-profile victims: Hustler magazine

The European Union Agency for Cybersecurity (ENISA) has found that 66 percent of supply chain attacks focus on the supplier’s code. Keep Reading

Additionally, the Committee favorable reported legislation that will enhance supply chain security, encourage made in America DHS uniforms, prevent acts of terrorism committed using rental vehicles, and improve cybersecurity in K-12 schools. Keep Reading

The study – which surveyed more than 300 cybersecurity leaders across Federal, state, and local government – found that 83 percent of public sector organizations operate on an ‘assume breach’ model today. Keep Reading

Entities worldwide can mitigate the vulnerabilities listed in this report by applying the available patches to their systems and implementing a centralized patch management system. Keep Reading

Under the Immigration and Nationality Act, a noncitizen who is likely to become a public charge is generally inadmissible to

The United States, in concert with the United Kingdom, is imposing additional costs on the Russian Federation on the one-year

If you don't recognize Franklin by his name, you will, most likely, recognize two of his high-profile victims: Hustler magazine

Biden also formally established the voluntary public-private partnership Industrial Control System Cybersecurity Initiative. Keep Reading

CISA has released an Industrial Control Systems (ICS) advisory detailing multiple vulnerabilities in multiple Geutebruck G-CAM E2 series devices and Encoder G-Code versions. Keep Reading

As part of CISA’s ongoing response to Pulse Secure compromises, CISA has analyzed 13 malware samples related to exploited Pulse Secure devices. Keep Reading
NSA’s Jason Wang, technical director for the Computer and Analytic Sciences Research Group, forecasted a future in which AI will support the Intelligence Community’s (IC) efforts to secure and defend our Nation’s networks. Keep Reading

These weaknesses are dangerous because they are often easy to find, exploit, and can allow adversaries to completely take over a system, steal data, or prevent an application from working. Keep Reading

Virginia Governor Ralph Northam has announced that the state has been awarded $1.5 million in federal funding to provide Virginia small businesses in the defense industry with required cybersecurity skills and certifications and help modernize the maritime industrial workforce. Keep Reading

A European survey from CWSI reveals that 54% of Irish companies have seen a rise in cybersecurity breach attempts in the last year, the highest in Europe and compared to 42% on average for European firms. Keep Reading

The overall mission of the program is to build cybersecurity resiliency and to harden the defenses of the U.S. and its strategic partners. The program enables actionable, relevant, and timely unclassified information exchange through trusted public-private partnerships across all critical infrastructure sectors. Keep Reading

Braintrace’s Network Detection and Response provides deep visibility into network traffic patterns, including encrypted traffic, without the need for Man-in-the-Middle decryption. Keep Reading

The president held an emergency cybersecurity meeting Thursday to weigh possible government action after reports that his mobile phone and those of government ministers may have been targeted by spyware. Keep Reading

In a statement, the firm said it had “obtained the tool from a third party and have teams actively helping customers affected by the ransomware to restore their environments, with no reports of any problem or issues associated with the decryptor”. Keep Reading
The United States — its public and private sectors — finds itself at a crossroads: we must improve our understanding of elusive, ever-changing threats, while simultaneously remaining agile in our capability to identify and respond to them. Keep Reading

The procurement shop at the National Institutes of Health has apparently satisfied several early complaints over the solicitation for the $50 billion CIO-SP4 IT services contract. Keep Reading
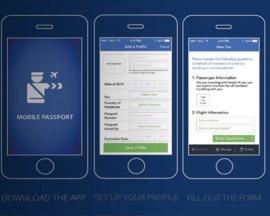
The Office of Inspector General (OIG) has found that U.S. Customs and Border Protection (CBP) did not always protect traveler data from cybersecurity risks, despite a responsibility to do so. Keep Reading
