Evanina: Combating China’s ‘Existential’ Cyber, Influence Threats Requires Post-9/11 Intensity
Eighty percent of U.S. adults have had all of their personal data stolen thanks to China's "persistent and unending resources." Keep Reading

Eighty percent of U.S. adults have had all of their personal data stolen thanks to China's "persistent and unending resources." Keep Reading
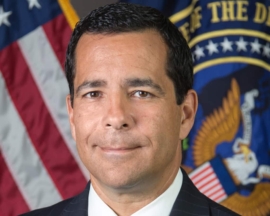
Evanina will provide his insight into the risks of intelligence collection and attack by foreign adversaries, in addition to his understanding of insider threats, personnel security, and supply chain threats. Keep Reading

Under the Immigration and Nationality Act, a noncitizen who is likely to become a public charge is generally inadmissible to

The United States, in concert with the United Kingdom, is imposing additional costs on the Russian Federation on the one-year

If you don't recognize Franklin by his name, you will, most likely, recognize two of his high-profile victims: Hustler magazine

Extremists reaping guidance online including information on using IEDs and small arms in attacks. Keep Reading

The average citizen is now being given information and knowledge management problems that would make history’s greatest generals shudder. Keep Reading

The Organization for Security and Co-operation in Europe (OSCE) has said it will not be able to send observers for the upcoming Russian parliamentary elections due to limitations imposed by Russian Federation authorities. Keep Reading

CISA is establishing the JCDC to integrate unique cyber capabilities across multiple federal agencies, many state and local governments, and countless private sector entities to achieve shared objectives. Keep Reading

Under the Immigration and Nationality Act, a noncitizen who is likely to become a public charge is generally inadmissible to

The United States, in concert with the United Kingdom, is imposing additional costs on the Russian Federation on the one-year

If you don't recognize Franklin by his name, you will, most likely, recognize two of his high-profile victims: Hustler magazine

A propensity of ethno-nationalist groups to conduct EI attacks appeared to increase over time in comparison to other ideologies. Keep Reading

Levine most recently served as a deputy assistant director of the Counterintelligence Division at FBI Headquarters in Washington. Keep Reading

National Security Agency Deputy Director George Barnes discussed NSA’s role within the nation’s shared response to future malicious cyber activities during Thursday’s Annapolis Cybersecurity Summit. Keep Reading

Several case studies about food adulteration, theft of intellectual property, and active shooter incidents by insiders in the food and agriculture sector are included in the document, as are links to additional resources from the federal government and other entities. Keep Reading

The campaign offers this package of pre-developed translated materials to provide meaningful access for individuals with limited English proficiency. Keep Reading
NSA’s Jason Wang, technical director for the Computer and Analytic Sciences Research Group, forecasted a future in which AI will support the Intelligence Community’s (IC) efforts to secure and defend our Nation’s networks. Keep Reading
The United States — its public and private sectors — finds itself at a crossroads: we must improve our understanding of elusive, ever-changing threats, while simultaneously remaining agile in our capability to identify and respond to them. Keep Reading

CAREERS & the disABLED magazine selected the National Security Agency as the 2021 Public-Sector Employer of the Year, a testament to the agency’s continued commitment to providing equal employment opportunities and fostering a fair and equitable work environment. Keep Reading

Moore most recently served as the special agent in charge of the Intelligence and Incident Response Division at the Washington Field Office. Keep Reading

I&A is expanding its intelligence and information analysis, production, and sharing capabilities; ensuring state and local partners have the information they need to protect their local communities, while also protecting privacy, civil rights, and civil liberties. Keep Reading

In the near-term, the company plans to focus this investment on accelerating key product initiatives and market innovations such as Flashpoint Flow, the company’s intelligence-specific automation platform, and the addition of new data sets that are critical to cyber threat intelligence, fraud, and physical security teams. Keep Reading

While experience fighting ISIS and al-Qaeda can be "directly relevant to countering REMVE, there are also significant differences that require new knowledge, approaches, strategies and tools." Keep Reading

Hackers "on the MSS payroll" made "a large ransom request made to an American company," senior administration official said. Keep Reading

The unit was allowed to abuse its authority for years without repercussions and became what whistleblowers described as a “gestapo" within the department that habitually targeted people of Chinese and Middle Eastern descent. Keep Reading
